What is Generative AI?
Generative AI is rapidly transforming numerous fields, from art and entertainment to healthcare and engineering. It represents a paradigm shift in how we create and interact with technology, moving from…
Active Reconnaissance: Techniques for Direct Information Gathering
Active reconnaissance is a crucial step in ethical hacking and cybersecurity. Unlike passive reconnaissance, which relies on publicly available information, active reconnaissance involves directly interacting with the target system to…
Passive Reconnaissance: Gathering Information from Public Sources
Passive reconnaissance is the initial phase of information gathering in ethical hacking and cybersecurity. It involves collecting information about a target without directly interacting with their systems. This approach minimizes…
Hands-on: Basic Network Scanning with Nmap
Nmap is a cornerstone tool for network administrators and ethical hackers alike. It allows you to discover hosts and services on a computer network by sending packets and analyzing the…
Introduction to Network Scanning Tools: Nmap
Network scanning is a fundamental skill for ethical hackers. It allows you to discover hosts and services on a network, which is the first step in identifying potential vulnerabilities. Nmap…
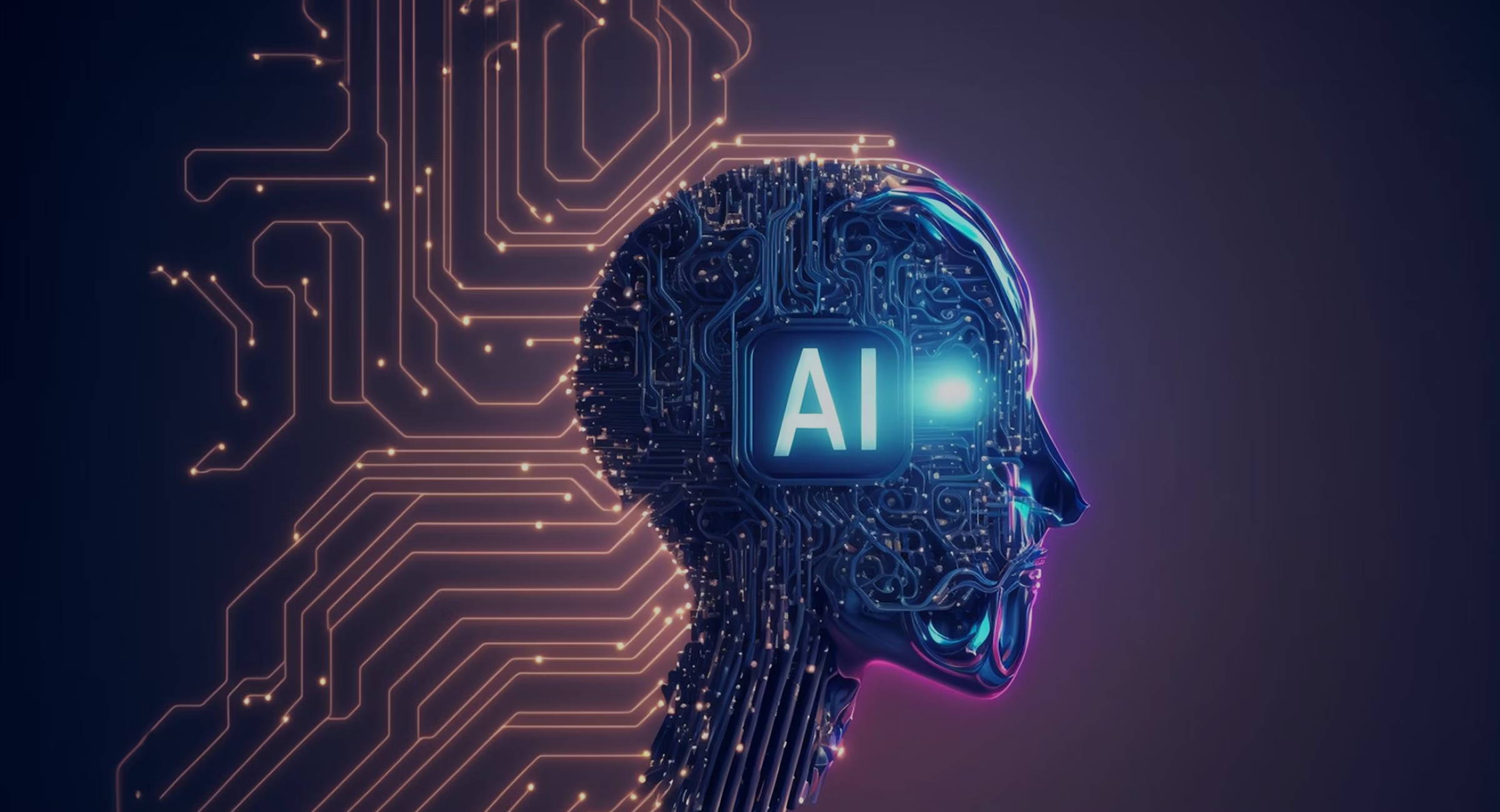
Network Topologies and Architectures
Network topologies and architectures are the fundamental building blocks of any network infrastructure. Understanding these concepts is crucial for ethical hackers as it allows them to visualize the network’s structure,…
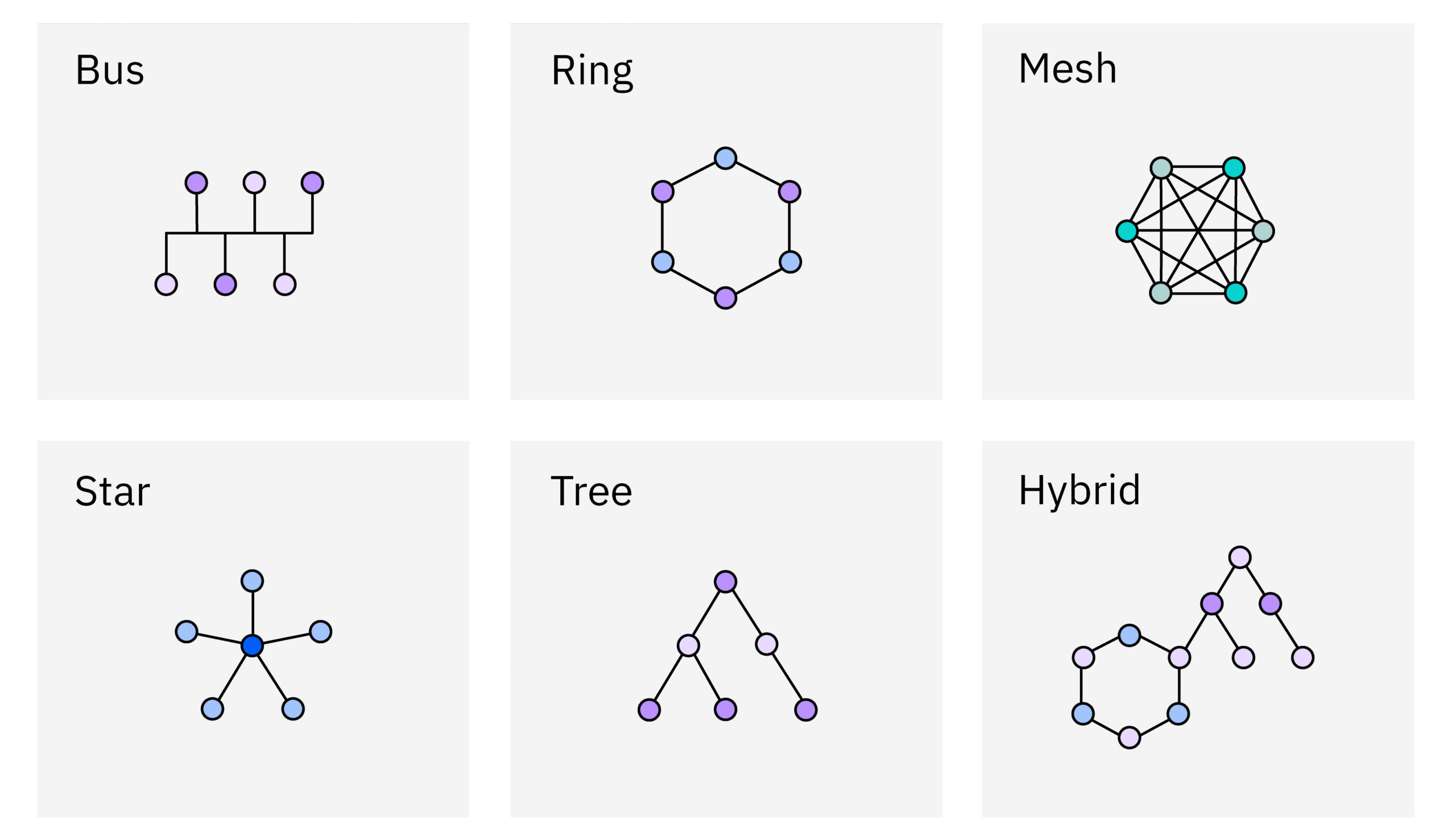
Common Network Protocols: HTTP, HTTPS, DNS, SMTP
Understanding network protocols is crucial for ethical hackers. These protocols are the languages that devices use to communicate, and knowing how they work allows you to identify vulnerabilities and potential…
MEXC Lists Doodles (DOOD) with 50,000 USDT Worth of DOOD and 50,000 USDT Bonus Prize Pool
The cryptocurrency exchange MEXC has made waves in the Web3 space with its May 9, 2025, listing of Doodles (DOOD), the native token of the beloved NFT-turned-entertainment brand Doodles. This move…
What is Software Architecture?
Software architecture is the fundamental organization of a software system, encompassing its components, their relationships to each other and to the environment, and the principles guiding its design and evolution.…
India-Pakistan Conflict: Live Updates on Military Strikes and Escalating Tensions
IntroductionTensions between India and Pakistan have reached a critical point following a deadly terror attack in Pahalgam, Jammu and Kashmir, on April 22, 2025, which claimed 26 lives, mostly tourists.…