Passive Reconnaissance: Gathering Information from Public Sources
Passive reconnaissance is the initial phase of information gathering in ethical hacking and cybersecurity. It involves collecting information about a target without directly interacting with their systems. This approach minimizes…
Getting Started with Bitcoin
Bitcoin is a revolutionary system that is quite complex and has a steep learning curve. Make sure you have a decent grasp of the system before you store a significant…
How to Read a Crypto Heat Map and Trade Futures & Options
Cryptocurrency trading has evolved beyond simple spot trading, with derivatives like futures and options gaining popularity. To make informed decisions, traders often use tools like crypto heat maps, which provide a…
Hands-on: Basic Network Scanning with Nmap
Nmap is a cornerstone tool for network administrators and ethical hackers alike. It allows you to discover hosts and services on a computer network by sending packets and analyzing the…
Dow Plummets Over 400 Points as Trump’s 50% EU Tariff Threat Sparks Market Jitters
IntroductionU.S. stock markets took a hit on Friday, May 23, 2025, as the Dow Jones Industrial Average fell more than 400 points in early trading. The sharp decline came in…
Introduction to Network Scanning Tools: Nmap
Network scanning is a fundamental skill for ethical hackers. It allows you to discover hosts and services on a network, which is the first step in identifying potential vulnerabilities. Nmap…
Bitcoin Shatters Records Above $110,000: Institutional Demand and Regulatory Shifts Fuel Crypto’s Historic Rally
May 22, 2025 The cryptocurrency market is witnessing an unprecedented surge as Bitcoin (BTC) continues its meteoric rise, breaching the $110,000 mark for the first time in history. This milestone…
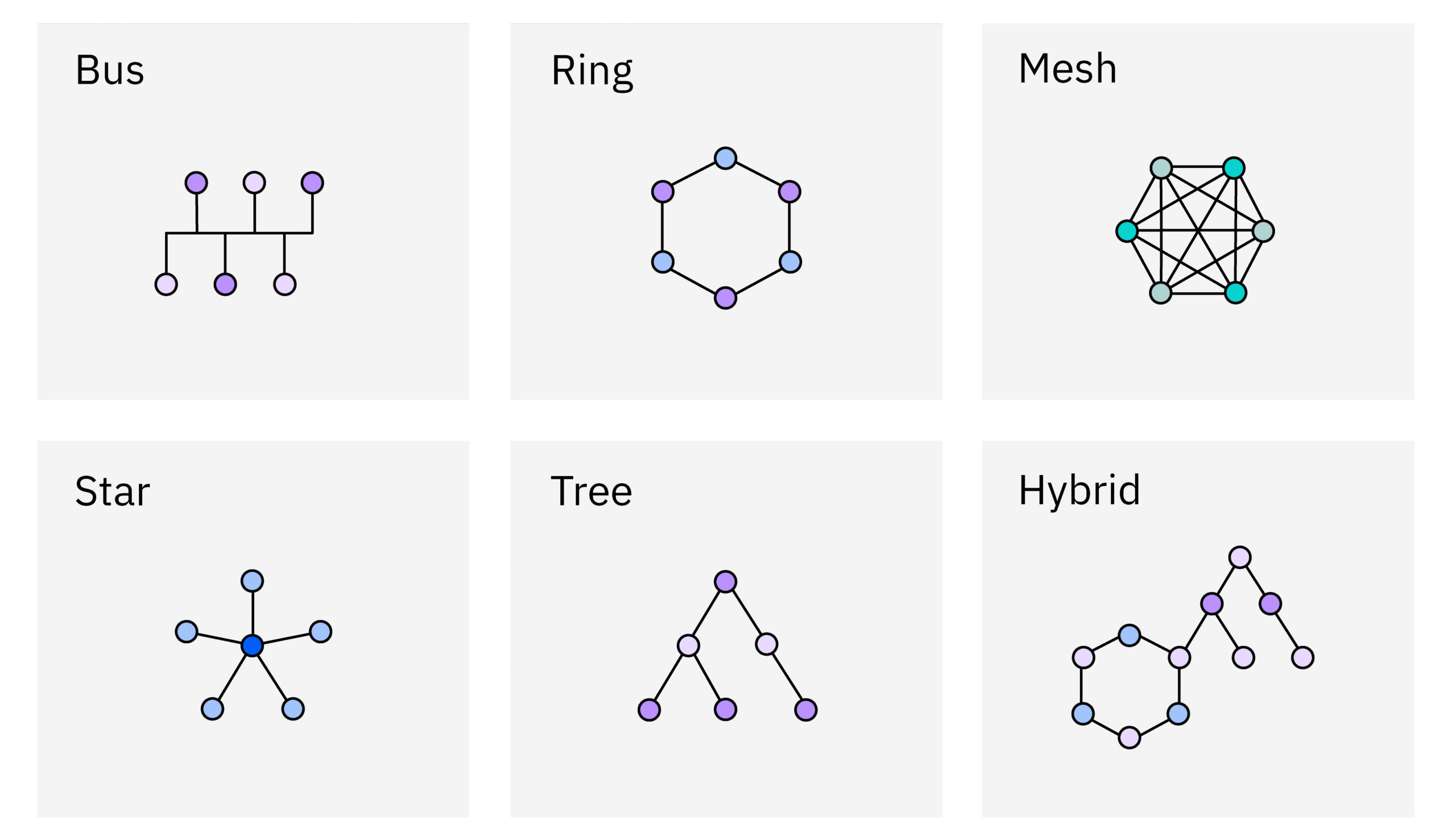
Network Topologies and Architectures
Network topologies and architectures are the fundamental building blocks of any network infrastructure. Understanding these concepts is crucial for ethical hackers as it allows them to visualize the network’s structure,…
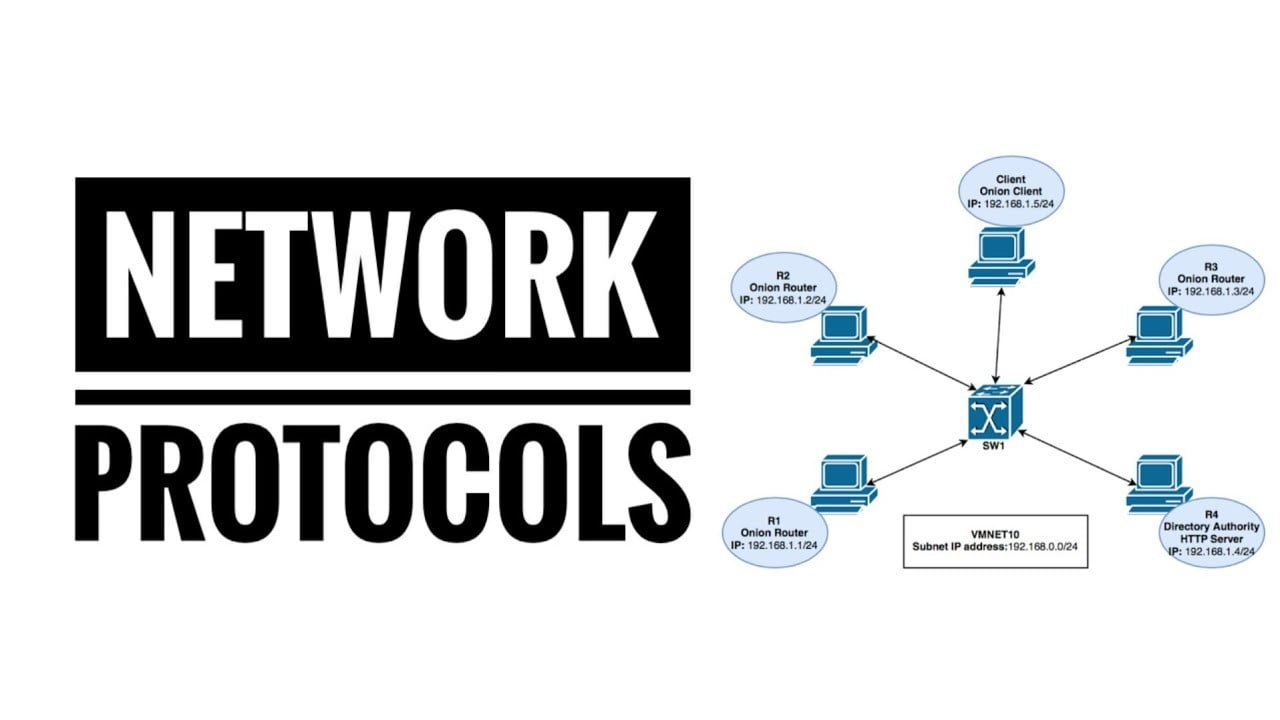
Common Network Protocols: HTTP, HTTPS, DNS, SMTP
Understanding network protocols is crucial for ethical hackers. These protocols are the languages that devices use to communicate, and knowing how they work allows you to identify vulnerabilities and potential…
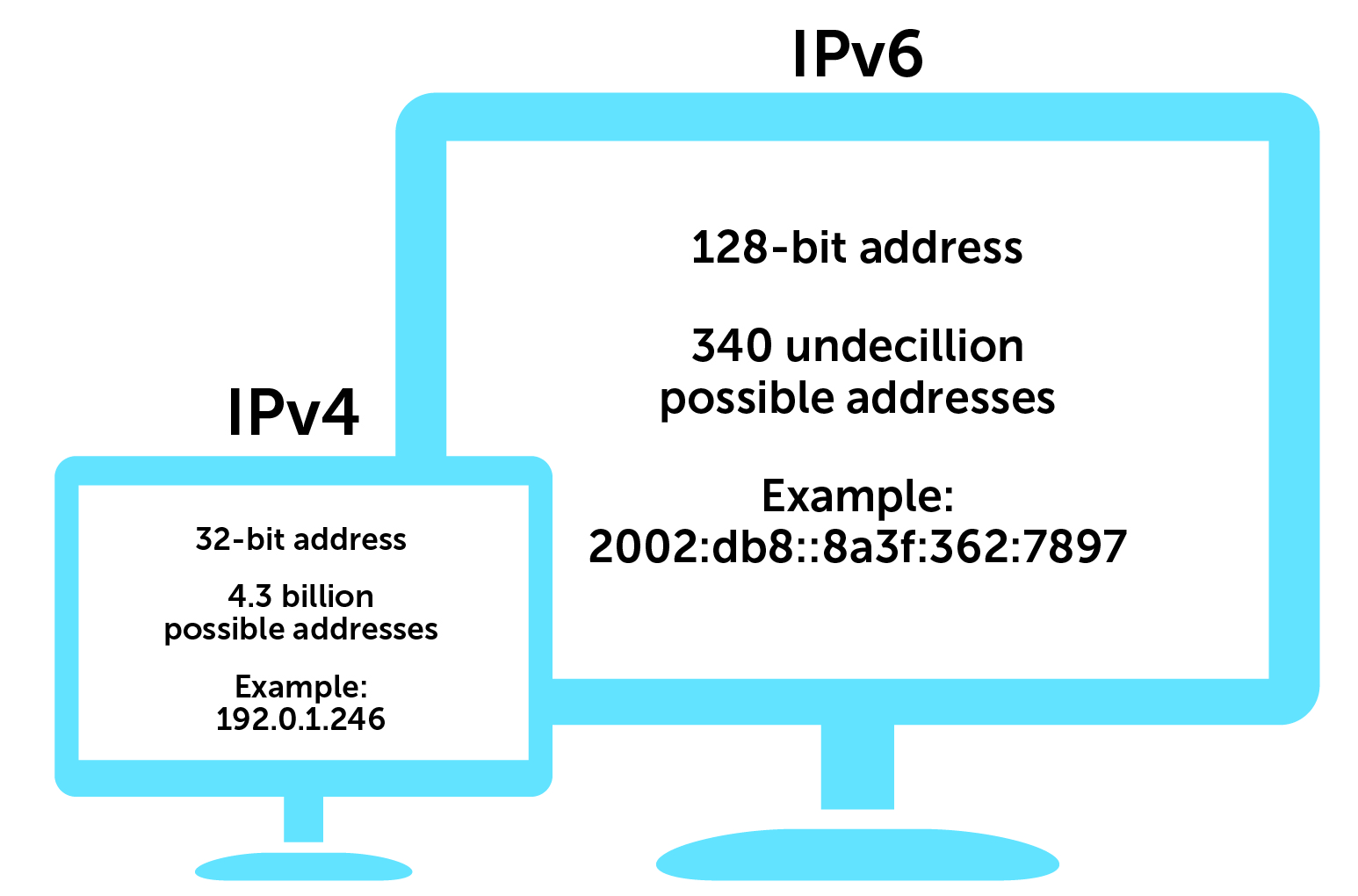
Understanding IP Addressing: IPv4 and IPv6
IP addressing is the backbone of network communication, enabling devices to identify and locate each other on a network. Understanding IP addresses, both IPv4 and IPv6, is crucial for ethical…
 India’s Unrest in 2025: Protests, Politics, and Media Coverage Amid Regional Tensions
India’s Unrest in 2025: Protests, Politics, and Media Coverage Amid Regional Tensions Generative AI and Angetic System: 7 Powerful Insights Transforming Technology
Generative AI and Angetic System: 7 Powerful Insights Transforming Technology GAN Structure: A Complete Guide to Generative Adversarial Networks
GAN Structure: A Complete Guide to Generative Adversarial Networks Mastering Vibe Coding: The Future of Creative and Technical Synergy
Mastering Vibe Coding: The Future of Creative and Technical Synergy Are Philips Hue Essential bulbs the cheap smart lights we don’t need?
Are Philips Hue Essential bulbs the cheap smart lights we don’t need? The Casabrews 5418 Pro is a super-affordable espresso machine, but too many corners have been cut to make it a good budget buy
The Casabrews 5418 Pro is a super-affordable espresso machine, but too many corners have been cut to make it a good budget buy I’ve tested 14 coffee makers in the last year, and these are my 3 favorite budget-friendly options
I’ve tested 14 coffee makers in the last year, and these are my 3 favorite budget-friendly options I’ve been eyeing the De’Longhi La Specialista Touch espresso machine – and now it’s got a 22% discount
I’ve been eyeing the De’Longhi La Specialista Touch espresso machine – and now it’s got a 22% discount Smeg’s new Mini Milk Frother prepares perfect foam for cappuccinos – but it’s too thick for latte art
Smeg’s new Mini Milk Frother prepares perfect foam for cappuccinos – but it’s too thick for latte art This quiet but powerful pedestal fan blew me away during testing – here’s why I’ve rated it 5 stars
This quiet but powerful pedestal fan blew me away during testing – here’s why I’ve rated it 5 stars