‘Who in the hell would want red cameras?’ – details of four new Nest devices have leaked, but has Google lost the smart home race already?
Amazon’s speakers, doorbells, and cameras will almost certainly be cheaper, but Gemini for Home could give Google an edge. Amazon’s speakers, doorbells, and cameras will almost certainly be cheaper, but…
Elon Musk’s xAI Embraces Open Source with Grok 2.5 Model Release
Elon Musk’s AI startup, xAI, has taken a bold step towards transparency and collaboration by officially open-sourcing its Grok 2.5 language model. This move signifies a strategic shift for the…
XRP Coin: Features, Team, and How to Monetize Your Investment in 2025
XRP is much more than just a cryptocurrency — it’s a powerful tool designed to revolutionize global payments. Created in 2012 by blockchain pioneers David Schwartz, Jed McCaleb, and Arthur…
Top Cryptocurrencies Under ₹1 in 2025: Hidden Gems with Strong Potential
Investing in cryptocurrencies priced below ₹1 (1 Indian Rupee) is a high-risk, high-reward game. Many investors dream of picking the next token that “explodes” in value just as Bitcoin and…
One of the best and cheapest video doorbells just plummeted to a great low price
The Blink Video Doorbell plummets to $39.99 at Amazon, which is a fantastic price for a cheap and capable smart doorbell that we love. The Blink Video Doorbell plummets to…
‘Why should I give Google money?’ – former Nest fans decry new leaked model, and I really can’t blame them
Google has given us a sneaky peek at a new Nest smart speaker, but what will it be, and do we really want it? Google has given us a sneaky…
The Ninja Double Stack air fryer is perfect for small kitchens and large families – and it’s now dropped below AU$400
With a AU$111 saving, this Nina Double Stack air fryer represents excellent value and is a fantastic deal to jump on if you’ve been eyeing up a top-performing air fryer. …
Swann’s new subscription-free home security camera stays charged with just 45 minutes of sunlight per day
The days of climbing up to replace batteries and paying monthly fees to save your video clips are over. The days of climbing up to replace batteries and paying monthly…
The Kuvings Hands-Free Slow Juicer AUTO10 Plus is the ultimate tool for juicing, and much more
Make large batches of juice, plus whip up sorbets, smoothies, sauces, plant milks, and more. Make large batches of juice, plus whip up sorbets, smoothies, sauces, plant milks, and more.
 India’s Unrest in 2025: Protests, Politics, and Media Coverage Amid Regional Tensions
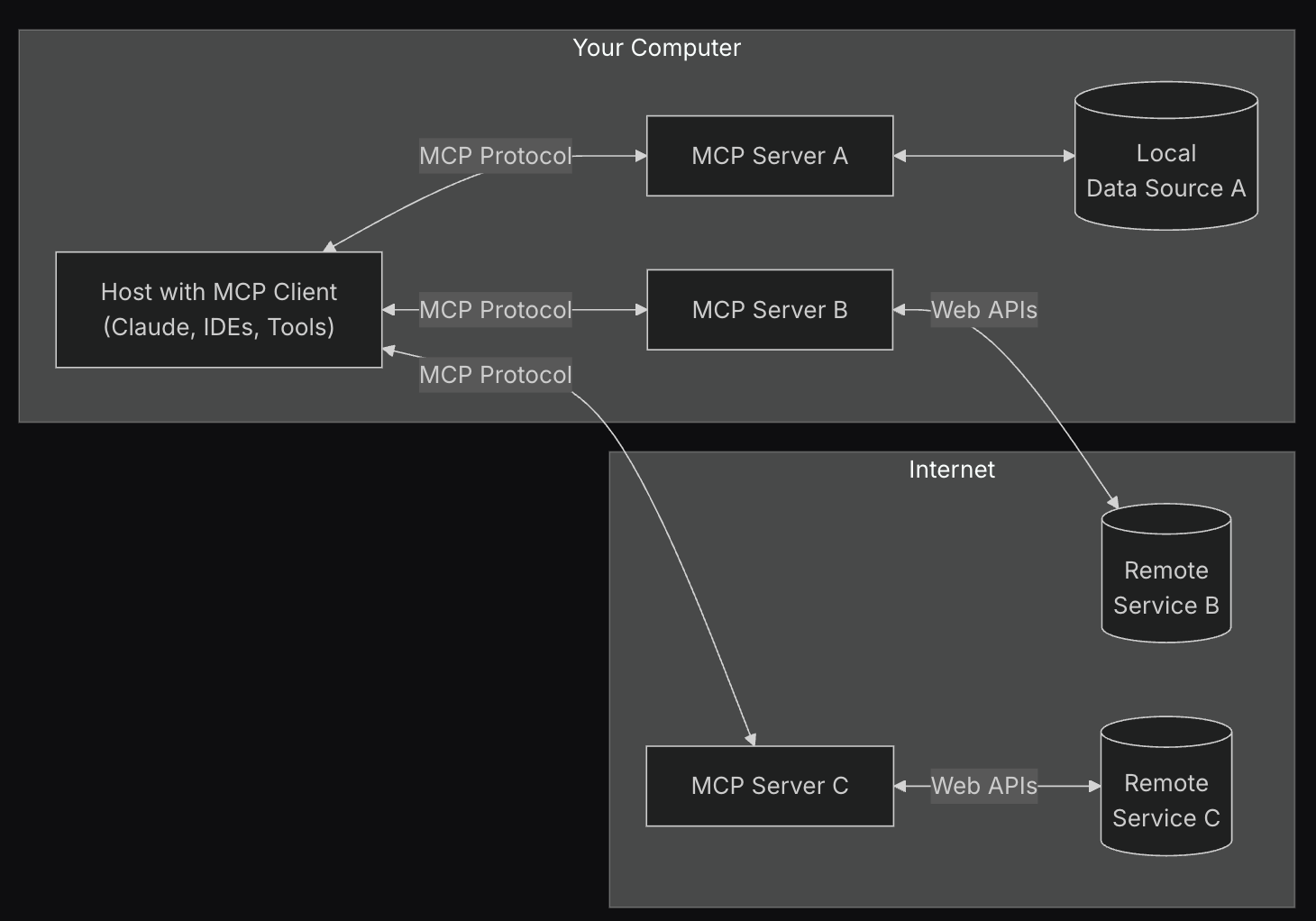
India’s Unrest in 2025: Protests, Politics, and Media Coverage Amid Regional Tensions Generative AI and Angetic System: 7 Powerful Insights Transforming Technology
Generative AI and Angetic System: 7 Powerful Insights Transforming Technology GAN Structure: A Complete Guide to Generative Adversarial Networks
GAN Structure: A Complete Guide to Generative Adversarial Networks Mastering Vibe Coding: The Future of Creative and Technical Synergy
Mastering Vibe Coding: The Future of Creative and Technical Synergy Are Philips Hue Essential bulbs the cheap smart lights we don’t need?
Are Philips Hue Essential bulbs the cheap smart lights we don’t need? The Casabrews 5418 Pro is a super-affordable espresso machine, but too many corners have been cut to make it a good budget buy
The Casabrews 5418 Pro is a super-affordable espresso machine, but too many corners have been cut to make it a good budget buy I’ve tested 14 coffee makers in the last year, and these are my 3 favorite budget-friendly options
I’ve tested 14 coffee makers in the last year, and these are my 3 favorite budget-friendly options I’ve been eyeing the De’Longhi La Specialista Touch espresso machine – and now it’s got a 22% discount
I’ve been eyeing the De’Longhi La Specialista Touch espresso machine – and now it’s got a 22% discount Smeg’s new Mini Milk Frother prepares perfect foam for cappuccinos – but it’s too thick for latte art
Smeg’s new Mini Milk Frother prepares perfect foam for cappuccinos – but it’s too thick for latte art This quiet but powerful pedestal fan blew me away during testing – here’s why I’ve rated it 5 stars
This quiet but powerful pedestal fan blew me away during testing – here’s why I’ve rated it 5 stars